THE DATA IS THE DIFFERENCE®
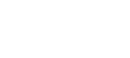
i360’s comprehensive data is a unique combination of hard data points and predictive modeling.

What sets i360's data apart?
i360’s comprehensive data is a unique combination of hard data points and predictive modeling. Our dataset incorporates extensive political identification, coalition, and membership information collected by way of in-person, phone, and online surveys, as well as through partner relationships, in addition to lifestyle and consumer data collected from multiple top-tier providers. Our data is further enhanced by our suite of predictive models, filling in gaps and helping us build the most complete profile for every individual possible.
INSIGHTFUL DATA
Gain insight through 1,800 unique data points on all 270 million Americans
i360’s proprietary, identity-verified consumer database provides clients with a rich demographic picture of the 270+ million adults in the US.
- 220M voters from all 50 states
- 270M + consumers, 100’s of data points
- Precinct election returns, Census, ACS, NOAA, BLS, geospatial data
- Membership, donor, customer, and affinity organizations
- Grassroots and paid phone, door, online, and event data

ACCURATE DATA
Build confidence in decisions through accurate independently sourced data
We don’t buy lists from data compilers that are likely outdated and inaccurate.
- Independently sourced voter data from every state and multi-sourced lifestyle data
- Partner with top-tier consumer providers prioritizing the accuracy and depth of every profile
- Data is constantly updated to ensure clients are receiving an accurate snapshot of the population
ACTIONABLE DATA
Take action with your data through state-of-the-art technologies
Our cutting-edge technologies empower our clients to turn data into results with ease.
- Easily create distinct audiences using robust search tools
- Build an efficient voter contact operation with i360 Walk, i360 Call, & i360 Text
- Expand your reach with digital segments and online action centers