WINNING MADE EASIER
i360 Portal v4 is your fully-integrated data & action management platform.
Winning made easier
The new Portal’s interface is modern and easier to use than ever. Google has been known for its best-in-class interface design and user experience. So, when it came time to build our new interface, we used Google’s front-end framework, Angular, and their Material Design system. Easily create custom audiences, import & export data, manage your contacts, create surveys, and visualize your results – all within one platform. Have multiple campaigns or organizations you’re working with? Single Sign On allows you to switch between accounts without having to log out.
Winning made smarter
Winning made faster
Searching your database is now 900% faster using a combination of ElasticSearch and AWS Aurora. File exports are now 10x faster using AWS serverless technologies. The time to route and publish surveys has been cut in half thanks to hundreds of microservices now supporting our system. And, with all of your data and tools in one place, you’ll spend less time switching between systems and more time engaging your audience.
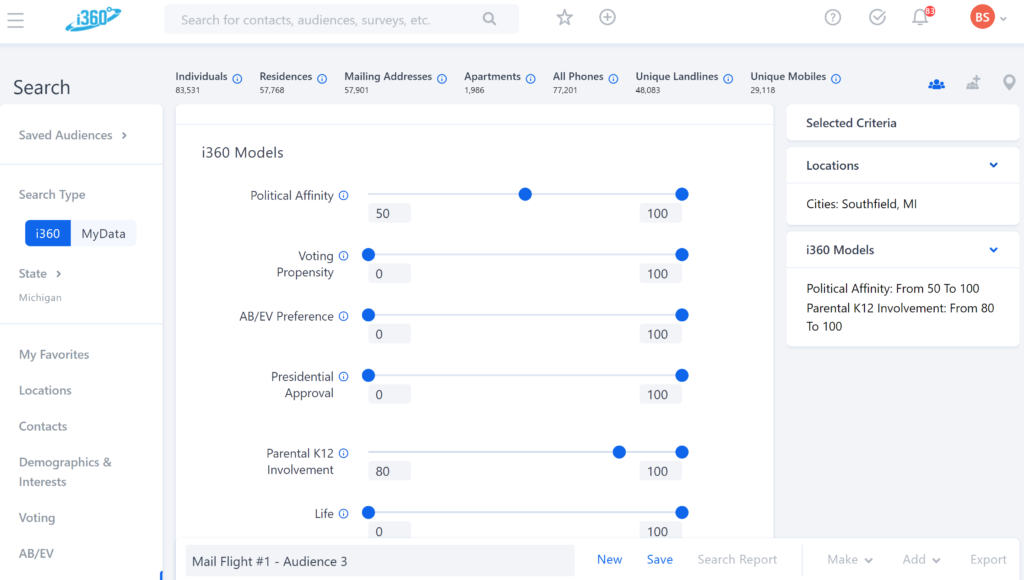
Audience Builder
Use our basic, advanced, and map search tools to easily define your audience with hundreds of data points, industry-leading predictive models, and your own tags. Create complex queries in seconds—not minutes—and without any coding. Once you’ve defined your universe, easily add it to a survey or action, or export lists for your mail program.
Custom Surveys
Those on the ground know best: Rather than forcing our clients to use a one-size-fits-all script, our survey builder allows for fully customizable scripts to collect the information you need, whether at the door, on the phone, or online. Easily collect binary data points like candidate support and yard sign requests, or save notes and add email addresses.
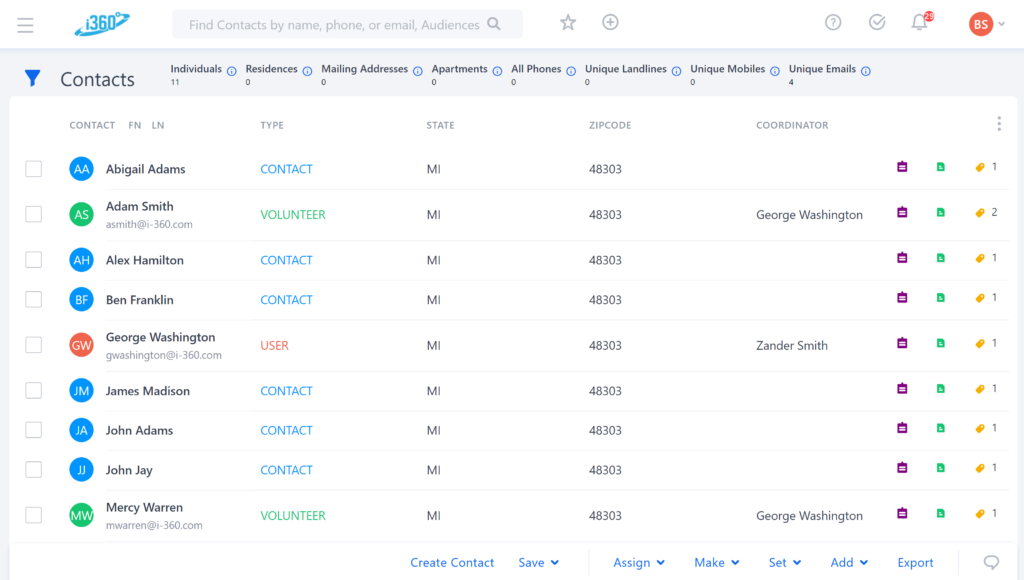
Volunteer Management
i360 doesn’t limit the number of volunteers that can access our apps. Instead, we empower our clients to easily manage their volunteers within the i360 Portal. Take advantage of customizable permission sets, view activity and history, and assign tasks down to individual walkbooks, call surveys, text actions, or online content.
Robust CRM
See a 360-degree view of your database including contact history, tags & notes, and individual data points on each record within your database. Call, text, and email individual voters right from their profile to seamlessly log every interaction.
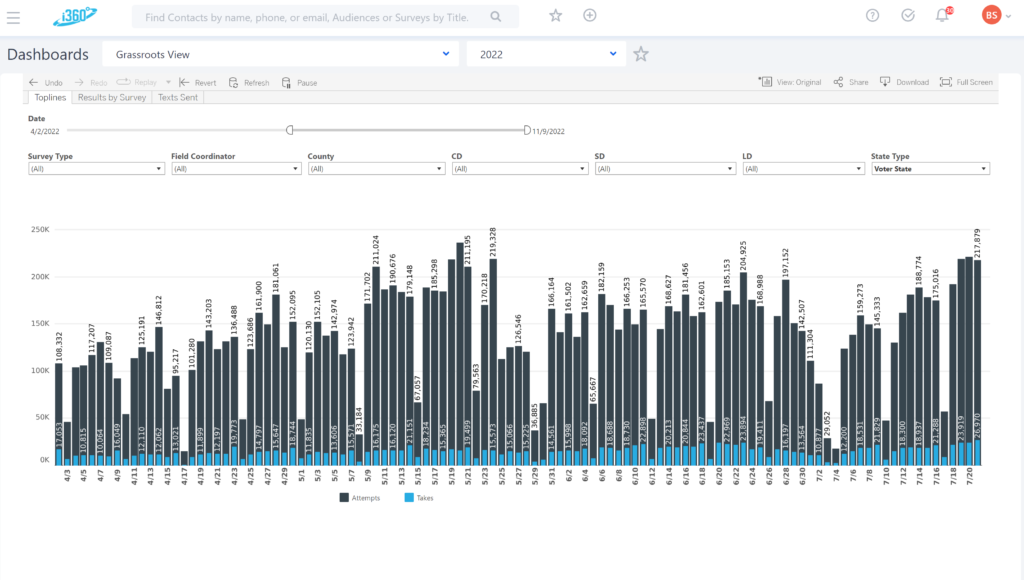
Integrated Dashboards
Stop wasting time exporting data to build custom spreadsheet reports. Quickly review your performance and results with our integrated dashboards. Have a custom need? Our experienced analytics team can build what you need.
Task Management
Scale your operations easily with our built-in task management tools. Assign tasks to other users, set reminders, and attach audiences to keep things on track.
Data Security
Since our founding in 2009, i360 has prioritized data security. Implementing safety measures like encryption, two-factor authentication, firewalls, intrusion detection, and penetration testing. We’ve long been committed to eliminating vulnerabilities and ensuring our clients’ data is secure.
SOC-2 Certified
i360 has maintained SOC-2 certification for years. Submitting to this continuous evaluation by third-party auditors is typically only done by major eCommerce companies that handle PII and credit data. i360 undergoes intensive audits conducted by certified auditors during which our systems and security controls are evaluated and tested for compliance with the AICPA. The review is exhaustive and comprehensive, examining everything from technical infrastructure and controls to HR protocols, policies, and personnel management to physical security including badge entry, visitor protocol, and video monitoring.
Industry Best Practices
To ensure our data is protected against attacks like SQL injection, cross-site scripting XXS, DDoS, and brute force, our technical team employs a range of best practices including:
- Employing a reverse proxy
- Web application firewalls
- Redundant, distributed systems
- Minimal surface area
- Strong encryption, no weak ciphers
- Machine learning-powered incident detection
Additional Measures
For extra protection, we conduct regular internal vulnerability scans and external black box and gray box testing and use multiple penetration testers to ensure we’ve covered all types of attacks. While many of the security procedures and controls required to qualify as compliant are time-intensive and expensive to implement and maintain, we believe they are critical and will do whatever it takes to keep your data safe.
